In Part 1, we talked basic computer science. I highly recommend reading/re-reading Part 1 before reading this article if you don’t have a firm grasp on the basics of computer science.
We’re going to start here in Part 2 by talking generically about some of the hurdles that cryptocurrencies have had to overcome, then we’ll define some terms, and finally we’ll put all the pieces together into a basic model of how a blockchain-based cryptocurrency works.
Traditional Ways of Passing Data through an Untrusted Medium
Let’s do a quick survey of a few ways that important data can be passed through an untrusted medium (i.e. the Internet). You’ll recognize some of these from Part 1.
Encryption
Pretend you have a secret message that you want to send from your computer to your friend’s computer. An easy example may be a message including your credit card information to purchase Glibertarians pink footie pajamas. How do you send that information from your computer, through a bunch of network devices (routers, switches, etc.) that are owned by neither you nor your friend, and to your friend without being intercepted by a nefarious third party?
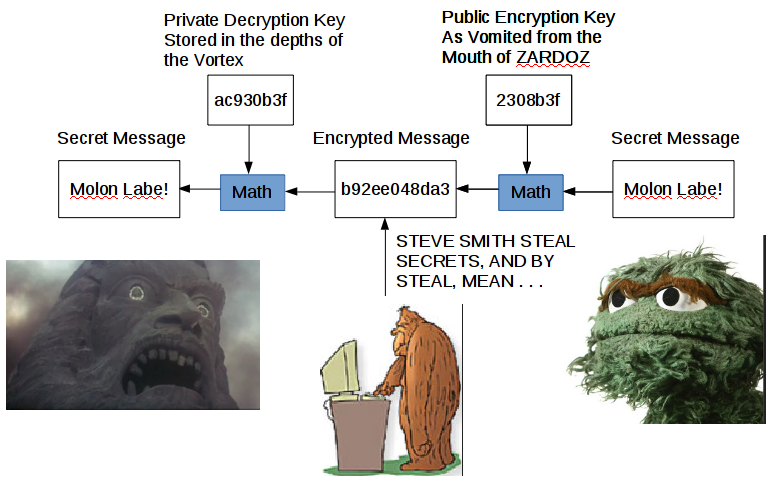
The easy answer is cryptography. Let’s change the message in a way that only your friend has the “key” to unchange it. There are many ways to do this, but one of the most common is public key cryptography. If you want more info on public key cryptography, check out Part 1.
Secured Channels
Sometimes, you’re sending a bunch of secret information across the network to the same place. The most common example is when you’re working from home. You’re transacting a bunch of secret information with your corporate servers, and it may be easier to just establish a secure channel between your computer and the corporate network so that you don’t have to manage the overhead of encrypting the info piecemeal. What am I describing? VPN.
This doesn’t really have anything to do with blockchain, but it gives you a bit of context about how security can be implemented over the Internet.
Trusted Authorities
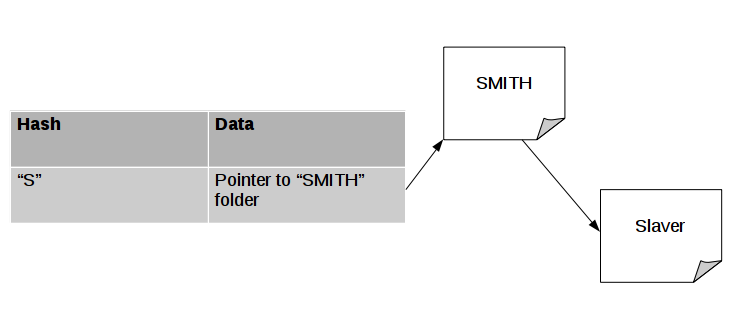
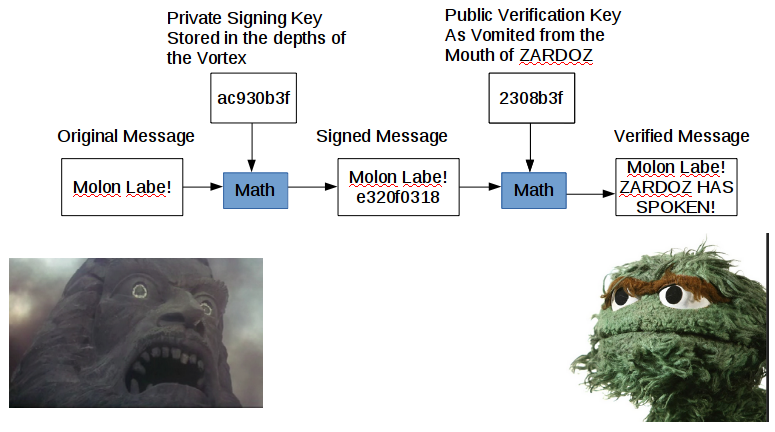
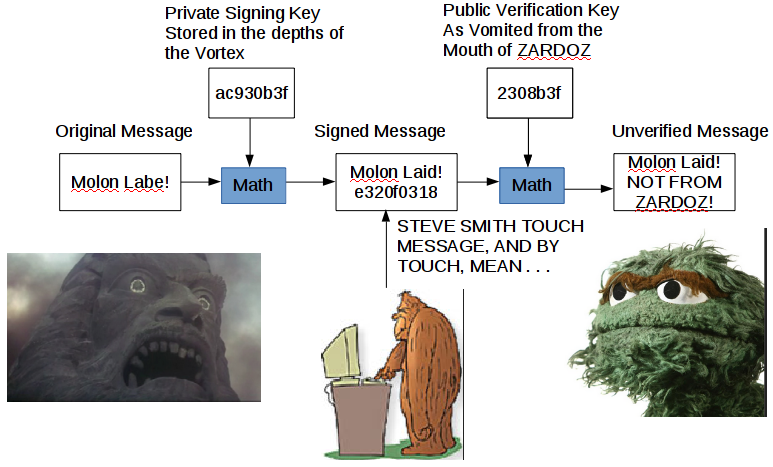
Trusted authorities also have nothing to do with blockchain, except to act as an opposing contrast to the way blockchain works. We talked in Part 1 about the two ways that public key cryptography can be used. One way is to securely send secret information across an untrusted link. Another way is to sign a message and validate that the message came from the person you think it did.
What if I want to know that you’re legit before I send you all my personal information? STEVE SMITH could easily insert himself between you and me, send me his public key, and then intercept and decrypt my response. This is called a “man in the middle” attack. Rather than just trust that the public key you supposedly sent me, I can reach out to a trusted 3rd party, who has your public key on file. I request your certificate from this trusted 3rd party (called the Certificate Authority), and compare the public key in the certificate with the public key you sent me to make sure it hasn’t been meddled with. The weakness of this method is that you have to trust the security of the Certificate Authority (the most well known CA is VeriSign).
Blockchain uses some of the encryption technologies we have discussed, but specifically cannot use VPN or CA technology because blockchain is implemented in a completely trustless environment. Why is it a trustless environment? Because authority is distributed rather than centralized.
Centralized, Decentralized, and Distributed: A Libertarian Way to Organize Things
I’m going to keep this focused to the tech realm, but y’all are smart enough to expand these concepts outside the realm of computers. There are three main ways of organizing tech in order to accomplish a task. Centralized systems involve everybody reaching out to one single node (e.g. server or cluster of servers) in order to accomplish the task. Decentralized systems involve everybody reaching out to one of a small number of nodes in order to accomplish the task. Distributed systems involve everybody reaching out to everybody else in order to accomplish the task.
Centralized
Centralized systems are what we use on an everyday basis. I want to buy something from Amazon, so I connect to an Amazon server and make the purchase. You want something from Amazon, so you connect to an Amazon server and make your purchase. This is a centralized system*, everybody connects with an Amazon server in order to complete their transaction.

* You could argue that Amazon runs a decentralized system, because there are Amazon servers all around the world to share the load of so many people shopping simultaneously. However, for this description, “centralized” refers to only one “entity” being involved, no matter the number of physical servers.
Decentralized
Decentralized systems are less common, but are still used on a regular basis. I want to refinance my house, so I go to LendingTree or any one of the other online insurance brokers. I input my information, which is sent to a handful of banks and other lenders, and each lender returns the request individually. If one lender doesn’t respond, it’s not quite as efficient, but I still have access to all of the other lenders.

Distributed
What if we take it a step further? Rather than a handful of entities, everybody can be an entity and everybody interacts with everybody. For example, Uber. You submit a ride request, and other people choose whether or not they want to fulfill that request. Uber isn’t perfectly distributed, as there is a barrier to entry before you can drive for Uber, but the barrier is low enough that it’s essentially distributed for our purposes.

How Transactions are Verified when Nobody can be Trusted
We have two obstacles to get over before we can verify a transaction. The first obstacle is ensuring that nobody has stepped in and altered a legitimate transaction. The second obstacle is ensuring that legitimate creator of the transaction isn’t trying some funny business.
We’ve already discussed a method for tackling the first obstacle, using public key signing. The person who is giving the money signs the transaction with their private key, and the public key is included in the transaction data. Then, anybody in the public can check the signature using the public key to make sure that the transaction was approved by the originator.
What about the second obstacle? Well, that’s a little more complicated and involves some economic incentives. We’ll get into this in more detail in Part 3 of this series, but suffice it to say that pulling off a con to steal somebody’s cryptocurrency involves an impossibly large amount of computer resources, and an immense amount of luck. The incentive to steal is way overridden by the costs of acquiring the raw processing power required to make such a con even remotely possible.
How does bitcoin get stolen, then? Usually some currency exchange website is hacked, and the private keys of users’ accounts (wallets) are compromised. It’s not a flaw in cryptocurrency, but in the exchange’s security. Blaming such hacks on cryptocurrency is like blaming the US Dollar because Chase’s system gets hacked.
Definitions and Terms of Art
Blockchain (Sometimes called distributed ledger technology) – A list of connected messages that contain transaction information. The blockchain is copied to every node (computer) in the blockchain network, allowing each and every participant in the blockchain to examine the blockchain for inconsistencies.
Cryptocurrency – A financial product that is transferred between people using a blockchain. Some people view cryptocurrencies as investment products (commodities). Others view cryptocurrencies as a currency. Many cryptocurrencies use a mathematical algorithm for “printing” new money that is rather deflationary, making them attractive long term investment vehicles.
Bitcoin – The original cryptocurrency that is trading for somewhere in the neighborhood of $11k per Bitcoin at the time of writing. You don’t have to buy full Bitcoins, but can buy as little as 0.0000001 Bitcoin.
Smart Contract – Some uses of blockchain are less tightly coupled to currency. Ethereum, for example, is a broader use blockchain system, and includes smart contracts, which are publicly inspectable contracts that are mostly self-executing. For example, if getting the wifi password is keyed to paying your rent, the smart contract will retain the new month’s wifi password and will not release it to the tenant until rent is paid.
Fork (of blocks in a chain) – A condition of the blockchain where two blocks are created and verified by different nodes in the network at substantially the same time. In such a situation, there is a “fork” until the next block is verified. Whichever forked block is retained by the node that verified the next block is the “winner”, ending the “fork.”
Fork (of cryptocurrencies) – A split off of a new cryptocurrency from an old one. Usually this happens because the older cryptocurrency has some limitation or flaw that the new cryptocurrency resolves. Depending on the specific situation, the older currency may transform into the new currency.
Merkle Tree – A type of binary tree (a hierarchical linked list where a “parent” node has at most two “children”) used to organize the cryptocurrency transactions stored within a block. Each leaf node (i.e. nodes without children) of the Merkle tree represents a transaction, and the parent nodes represent a combination of multiple transactions. Each node has a hash, with the root node (the parent of all parents) containing a transaction hash for the entire block. These hashes can be used to verify the accuracy of the transactions, and the transaction hash for the entire block is used in creating the hash for the block.
Wallet – A data structure built around a user’s private key that retains all of the cryptocurrency that has been transferred to it.
Exchange – A website that retains a cryptocurrency wallet for each of its users. Exchanges are like a cross between a bank and an investment broker.
Blockchain? Is That Some New Type of Jewelry?
Blockchain is the technical underpinning of cryptocurrencies. A blockchain is a linked list of data structures. Each data structure includes a header, a transaction ledger, and a pointer to the prior block.
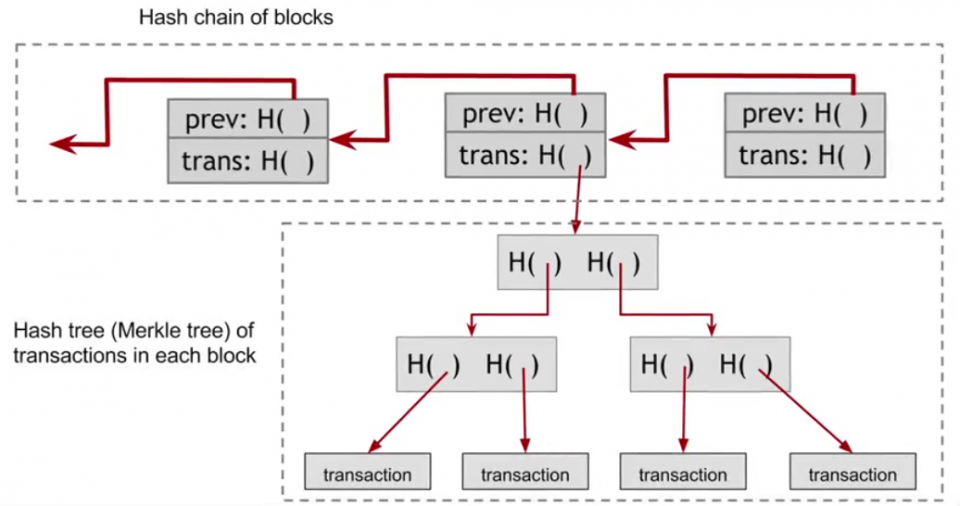
Here is a very high-level view of what a blockchain looks like. You have ledger of transactions arranged in a tree form (a tree is a linked data structure kind of like a linked list, but with more than one relationship saved in the structure. For example, in a binary tree, each “parent” data structure has two “children”). The actual transactions are located in the leaf nodes (a leaf node has no children), and the root is the top parent node. The Merkle tree (the specific type of binary tree used for blockchain transactions) calculates the hash of each transaction, and then continues to hash the combined hashes up the tree until we get what’s called the Merkle root hash (shown as “trans: H( )”). The specifics of how all this works isn’t super important, and it’s fairly intuitive once you understand hashing. You’re essentially taking hashes of hashes until you get one single hash that represents all of the transactions in the block. Why do we want that?
Because the hash of the block (used for security/verification purposes) isn’t the hash of the ENTIRE block, but only of the header of the block. The actual transactions and the Merkle tree are contained in the transaction ledger, and are not taken into account when calculating the hash of the block. However, the Merkle root hash (which takes into account all of the transactions) is located in the header of the block and is thus taken into account when calculating the hash of the header of the block. If a nefarious actor tried to change one of the transactions to route currency to his wallet, it would change the Merkle root hash, which would change the hash of the block, resulting in it being obvious to the blockchain network that something has been tampered with. We’ll go into more detail on this in Part 3 of the series.
The last concept I want to bring up in this article is the increasing security over time. How does that work? Well, it has to do with the linked list of blocks. Let’s say we have three blocks that STEVE SMITH wants to corrupt in order to steal some cryptocurrency.
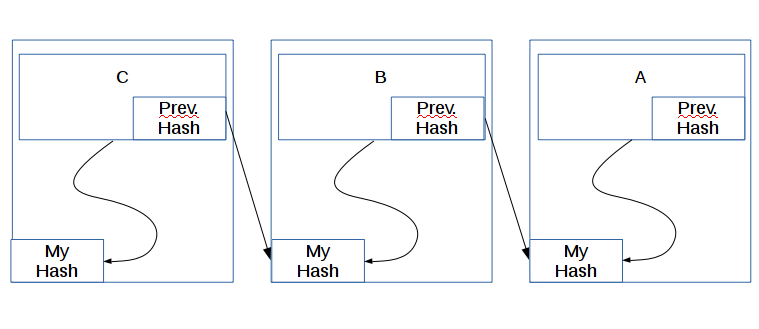
STEVE SMITH will have the easiest time corrupting block C. Why? Because all he has to do is change the transactions and calculate the new hash for C. I say “all he has to do” as if it’s easy. We’ll talk in Part 3 about why this is nearly impossible to do. However, let’s assume for a moment that STEVE SMITH has a ton of computing resources and it isn’t quite nearly impossible to corrupt C anymore. Now, let’s see why the older a block is, the harder it is to corrupt.
STEVE SMITH sees a huge transaction of cryptocurrency in block A and wants it for himself. In order to pull of his heist, he alters the transaction in block A, but now A’s “My Hash” is wrong (we’ll discuss tomorrow how the network knows it’s wrong). STEVE SMITH then spends a bit of time calculating A’s correct new My Hash. Once that’s done, there’s still a problem. B’s “Prev. Hash” is wrong, and the network will see the obvious inconsistency. STEVE SMITH changes B’s Prev. Hash to match A’s My Hash. Great! All fixed!
But wait! B’s My Hash is calculated in part using B’s Prev. Hash, so now B’s My Hash is glaringly wrong. With a sigh of frustration, STEVE SMITH begins the time intensive process of calculating B’s new My Hash. STEVE SMITH, being one of the smartest of his race, sees that block C is going to have the same issue, so he quickly updates C’s Prev. Hash after figuring out B’s My Hash, and begins cranking on C’s My Hash. Finally, after a bit of time, STEVE SMITH has updated the blockchain and his crime was a success!!
Or not. See, while he was cranking hard calculating new hashes for three blocks, the blockchain network was adding new blocks every few minutes (10 minutes for Bitcoin). His fraud sticks out like a sore thumb because blocks D through L all have the wrong hash when his “modified” blocks are included. In order for STEVE SMITH to succeed in his nefarious plan, he would need to control a significant portion of the entire world’s computing power, something on the order of 45% of the blockchain would need to be controlled to give his plan even a dismal chance.
I’m going to stop here. We’re going to dive down to a place where giant octopi and fish with bioluminescent lures live in Part 3. We’ll discuss the details of how hashing is extensively used in the blockchain, how incentives are used to increase security through mining, how blockchain can be used outside of cryptocurrency, a description of the major cryptocurrencies and what they’re useful for, and some of the drawbacks of cryptocurrencies.









 Jimmy Carter Deregulates The Business End of Trucking
Jimmy Carter Deregulates The Business End of Trucking The late 1980’s and early 1990’s saw a massive increase in the competition in the trucking marketplace, which also saw the growth of 3PL’s, also known as load brokers. Many more new companies were opening, many more independent owner/operators were hitting the roads, and the marketplace continued to evolve. Things at the operational end of the business, however, were also evolving, and not always in a good way.
The late 1980’s and early 1990’s saw a massive increase in the competition in the trucking marketplace, which also saw the growth of 3PL’s, also known as load brokers. Many more new companies were opening, many more independent owner/operators were hitting the roads, and the marketplace continued to evolve. Things at the operational end of the business, however, were also evolving, and not always in a good way. The split sleeper provision, such as it was, was the tool in our HOS regimen which gave us the flexibility to meet the demands of life on the road, shipping schedules, traffic, you name it. If you were held up at a customer, unpaid and with nothing you could possibly do about it,
The split sleeper provision, such as it was, was the tool in our HOS regimen which gave us the flexibility to meet the demands of life on the road, shipping schedules, traffic, you name it. If you were held up at a customer, unpaid and with nothing you could possibly do about it,  And there are millions of situations like this taking place every day, in every subdivision of the trucking industry. Imagine being a cattle hauler, and you have a full load of calves on board, and it’s winter time. You run out of your 11 hours driving time, and have to stop, in the middle of winter, most likely at a location where you can’t unload your cargo and get them inside somewhere where they won’t freeze to death. Or imagine that you are me, or one of the many other people who used to run The Ice up North (remember
And there are millions of situations like this taking place every day, in every subdivision of the trucking industry. Imagine being a cattle hauler, and you have a full load of calves on board, and it’s winter time. You run out of your 11 hours driving time, and have to stop, in the middle of winter, most likely at a location where you can’t unload your cargo and get them inside somewhere where they won’t freeze to death. Or imagine that you are me, or one of the many other people who used to run The Ice up North (remember  For the liberty minded professional driver, the situation looks bleak. I doubt very highly that the FMCSA is ever going to change the HOS regulations to match more humane and productive provisions in places like Canada or New Zealand, where a guy can drive 13 hours a day and, at least in Canada, has a bit more flexibility with shifting hours around. And I also doubt very highly that the FMCSA or any state level DOT is going to give up on the rolling cash cows that are ELDs. If you are an owner operator and you have a truck with a model year older than 2000, you are exempt from the ELD mandate, but that doesn’t help with the stupid HOS regs, and many large carriers won’t take on owner operators who choose to run older equipment. (And don’t get me started on the EPA rules and how they have completely screwed up the engine marketplace, such that Caterpillar quit making on-highway diesel engines. Another article entirely …. ) Trucking is an ultra-competitive marketplace for rates, and the little guy has an enormous hill to climb in competing against legacy carriers, who benefit both from economics of scale, and being large enough to enjoy the privileges of regulatory capture. Hell, some of these arseholes, through cronyist organizations like The American Trucking Association, go right along with all of these stupid laws because they know they can comply with them. The Provinces of Ontario and Quebec instituted mandatory truck speed limiters, restricting trucks to 105km/h (65mph) by law, even for carriers not based there. These rules were not proposed by the Ontario Ministry of Transport, or it’s analogs in Quebec; they were proposed by mega-carriers like Challenger Motor Freight, and their crony mouthpieces in the Ontario Trucking Association.
For the liberty minded professional driver, the situation looks bleak. I doubt very highly that the FMCSA is ever going to change the HOS regulations to match more humane and productive provisions in places like Canada or New Zealand, where a guy can drive 13 hours a day and, at least in Canada, has a bit more flexibility with shifting hours around. And I also doubt very highly that the FMCSA or any state level DOT is going to give up on the rolling cash cows that are ELDs. If you are an owner operator and you have a truck with a model year older than 2000, you are exempt from the ELD mandate, but that doesn’t help with the stupid HOS regs, and many large carriers won’t take on owner operators who choose to run older equipment. (And don’t get me started on the EPA rules and how they have completely screwed up the engine marketplace, such that Caterpillar quit making on-highway diesel engines. Another article entirely …. ) Trucking is an ultra-competitive marketplace for rates, and the little guy has an enormous hill to climb in competing against legacy carriers, who benefit both from economics of scale, and being large enough to enjoy the privileges of regulatory capture. Hell, some of these arseholes, through cronyist organizations like The American Trucking Association, go right along with all of these stupid laws because they know they can comply with them. The Provinces of Ontario and Quebec instituted mandatory truck speed limiters, restricting trucks to 105km/h (65mph) by law, even for carriers not based there. These rules were not proposed by the Ontario Ministry of Transport, or it’s analogs in Quebec; they were proposed by mega-carriers like Challenger Motor Freight, and their crony mouthpieces in the Ontario Trucking Association. Bitcoin’s foundation is a public transaction ledger called the blockchain. Every bitcoin transaction is recorded on the blockchain and anyone can inspect the transaction history going back to the creation of the first block of the chain. Because the blockchain is public, bitcoin transactions are not as anonymous as some people currently in prison had hoped. Every new account is anonymous, but that anonymity will probably be compromised by the first transfer of bitcoin into it because the bitcoins in the source account probably have a history–and there are companies whose business plan is to delve through the blockchain to link accounts to owners and sell the information.
Bitcoin’s foundation is a public transaction ledger called the blockchain. Every bitcoin transaction is recorded on the blockchain and anyone can inspect the transaction history going back to the creation of the first block of the chain. Because the blockchain is public, bitcoin transactions are not as anonymous as some people currently in prison had hoped. Every new account is anonymous, but that anonymity will probably be compromised by the first transfer of bitcoin into it because the bitcoins in the source account probably have a history–and there are companies whose business plan is to delve through the blockchain to link accounts to owners and sell the information.

 Also worth noting is the point he’d made earlier about employees being replaced by automation if they get too expensive to employ. This is a very valid point that most minimum wage workers and people who advocate for them don’t seem to understand. Again, people own businesses to make themselves money. If they can’t make enough money, something’s got to give. And when there’s no more non-employee overhead to cut, they need to start cutting people. As a general rule of thumb, it costs about twice an employee’s gross pay to employ them (given employer shares of FICA, certain states’ income tax, worker’s comp, benefits, etc.)… so that $10k/yr employee actually costs the business owner around $20k. I’d imagine Obamacare penalties and/or post-obamacare insurance premiums have upped that 2:1 ratio. So if it costs less than $20k/yr to set up an automated ordering kiosk and a burger flipping robot, guess what a business owner is going to do?
Also worth noting is the point he’d made earlier about employees being replaced by automation if they get too expensive to employ. This is a very valid point that most minimum wage workers and people who advocate for them don’t seem to understand. Again, people own businesses to make themselves money. If they can’t make enough money, something’s got to give. And when there’s no more non-employee overhead to cut, they need to start cutting people. As a general rule of thumb, it costs about twice an employee’s gross pay to employ them (given employer shares of FICA, certain states’ income tax, worker’s comp, benefits, etc.)… so that $10k/yr employee actually costs the business owner around $20k. I’d imagine Obamacare penalties and/or post-obamacare insurance premiums have upped that 2:1 ratio. So if it costs less than $20k/yr to set up an automated ordering kiosk and a burger flipping robot, guess what a business owner is going to do? In this country, like most countries in the world, we have a fiat currency; that is, a currency whose value is not linked to a commodity (like gold, silver, or salt), but is based on the trust that the country issuing the currency can pay its bills. By its nature, fiat currencies are subject to almost constant inflation through devaluation of the currency. Especially when the country in question is engaging in… let’s say non-optimal monetary and economic practices. In our case, budget deficits, a high national debt, and things like quantitative easing. It’s part of the reason everyone’s parents have stories of “I remember when gas was $0.35!” (for my generation’s parents) or “I remember when gas was $0.98!” (the story I get to tell if/when I have kids and they’re old enough to be regaled with tales of ‘the good old days’). Another factor in inflation is artificially raising wages– you’ve arbitrarily decided that the dollar is worth less than it is, so people need more of them. And by deciding that one segment of the population needs more, less valuable dollars, everyone else needs to have and spend more, less valuable dollars to keep up with the sudden devaluation of a dollar for a certain segment of the population.
In this country, like most countries in the world, we have a fiat currency; that is, a currency whose value is not linked to a commodity (like gold, silver, or salt), but is based on the trust that the country issuing the currency can pay its bills. By its nature, fiat currencies are subject to almost constant inflation through devaluation of the currency. Especially when the country in question is engaging in… let’s say non-optimal monetary and economic practices. In our case, budget deficits, a high national debt, and things like quantitative easing. It’s part of the reason everyone’s parents have stories of “I remember when gas was $0.35!” (for my generation’s parents) or “I remember when gas was $0.98!” (the story I get to tell if/when I have kids and they’re old enough to be regaled with tales of ‘the good old days’). Another factor in inflation is artificially raising wages– you’ve arbitrarily decided that the dollar is worth less than it is, so people need more of them. And by deciding that one segment of the population needs more, less valuable dollars, everyone else needs to have and spend more, less valuable dollars to keep up with the sudden devaluation of a dollar for a certain segment of the population. Myth #2: “It’s based on nature, not arbitrary units”
Myth #2: “It’s based on nature, not arbitrary units” So what is the metric system if none of those myths? It’s the product of a decimal fetishist. Which is frankly a pretty low grade of fetish. It’s like being preferentially attracted to Americans while you’re vacationing in Prague. Prague, Czech Republic, not Prague, Oklahoma. They’re not even pronounced the same. The metric system was made by shallow-thinking revolutionaries who thought themselves wise. For them, the decimal system had totemic value, like black guns or Maggie McNeil’s “sex rays.” Their cook could understand halves and thirds, and quarters, but it took a man of the proper social class to understand 3/10ths. All the good things about the metric system happen because it’s tied to the decimal system. Which is also its biggest problem, because the decimal system is pretty crap. But in one of the most unfortunate examples of existence bias in history, Messrs. Haut-Hommes never considered that maybe the decimal system was what they needed to take forth on the tumbrel.
So what is the metric system if none of those myths? It’s the product of a decimal fetishist. Which is frankly a pretty low grade of fetish. It’s like being preferentially attracted to Americans while you’re vacationing in Prague. Prague, Czech Republic, not Prague, Oklahoma. They’re not even pronounced the same. The metric system was made by shallow-thinking revolutionaries who thought themselves wise. For them, the decimal system had totemic value, like black guns or Maggie McNeil’s “sex rays.” Their cook could understand halves and thirds, and quarters, but it took a man of the proper social class to understand 3/10ths. All the good things about the metric system happen because it’s tied to the decimal system. Which is also its biggest problem, because the decimal system is pretty crap. But in one of the most unfortunate examples of existence bias in history, Messrs. Haut-Hommes never considered that maybe the decimal system was what they needed to take forth on the tumbrel.








 years of the Indianapolis 500, the race and the supporting series were based on a free-market-style “run what you brung” model, resulting in a rich and storied tradition. Stories of
years of the Indianapolis 500, the race and the supporting series were based on a free-market-style “run what you brung” model, resulting in a rich and storied tradition. Stories of  As can be easily predicted by those of us familiar with the stories of Soviet Russia, Venezuela, Cuba, and North Korea, IndyCar has been suffering from poor racing, fewer teams, fewer race cars, and an utter collapse of the fanbase. Besides a single day per year burning off 75 years of tradition, American Open-Wheel Racing is on life support. Of course, these are “bad economic times” and “motorsports is on a decline” and “we can’t afford competition.” The excuses have been flying since 1996 when they first headed down this path. Every half-hearted, feeble attempt to introduce a market influence is quickly undone. The toe in the water is withdrawn as soon as they realize it’s wet.
As can be easily predicted by those of us familiar with the stories of Soviet Russia, Venezuela, Cuba, and North Korea, IndyCar has been suffering from poor racing, fewer teams, fewer race cars, and an utter collapse of the fanbase. Besides a single day per year burning off 75 years of tradition, American Open-Wheel Racing is on life support. Of course, these are “bad economic times” and “motorsports is on a decline” and “we can’t afford competition.” The excuses have been flying since 1996 when they first headed down this path. Every half-hearted, feeble attempt to introduce a market influence is quickly undone. The toe in the water is withdrawn as soon as they realize it’s wet.